What is ISO/IEC 27011?

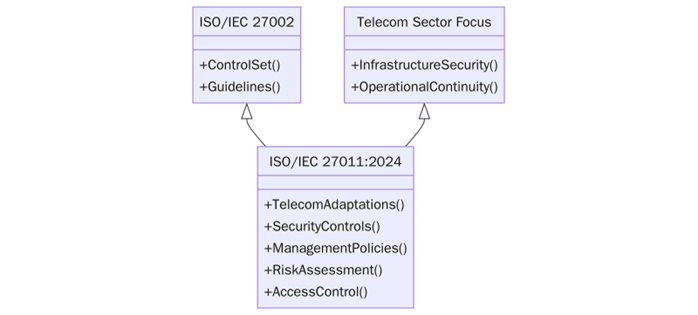
ISO/IEC 27011:2024 is a sector-specific standard that adapts the controls from ISO/IEC 27002 for use within the telecommunications industry. It provides detailed implementation guidance that aligns with the broader ISO/IEC 27001 information security management framework, but tailors these practices to the specific risks and requirements of telecom operations.
This standard helps telecommunications providers establish, implement, maintain, and improve information security measures, ensuring the confidentiality, integrity and availability of data across voice, messaging, data and mobile services.
To discuss certification or schedule an audit, contact us at support@pacificcert.com
Purpose
The purpose of ISO/IEC 27011:2024 is to help telecommunications organisations implement tailored security controls that match the risks and technological complexities inherent in the telecom industry. The standard supports the need for continuous service availability, network stability, and lawful interception. It also offers structured guidance on managing confidentiality and integrity of communications across complex and distributed infrastructures.

Telecom operators deal with large volumes of sensitive user data and operate systems that are critical to national infrastructure. ISO/IEC 27011 helps ensure these services are protected against evolving cyber threats.
Scope and Applicability
This standard is applicable to all types of telecommunications organisations, including fixed and mobile network providers, satellite and cable operators, and internet service providers. It is also relevant to regulatory bodies and entities offering cloud-based telecom services. Whether the organisation is small, national or multinational, ISO/IEC 27011 helps establish appropriate security controls based on operational scale, risk level and regulatory expectations.
The standard supports integration with existing management systems such as ISO/IEC 27001 and ISO 9001, making it suitable for telecom firms pursuing aligned compliance and business objectives.
Key Definitions
- Information Security Management System (ISMS): A systematic approach for managing sensitive company information to remain secure.
- Telecommunications Environment: Includes switching systems, transmission networks, data centres, customer premises equipment, and operational support systems.
- Control Objectives: Goals that security controls are intended to achieve to mitigate identified risks.
- Asset Classification: Grouping assets by their importance to information security and risk exposure.
Clause-wise Structure of ISO/IEC 27011
Clause | Title |
| Description |
1 | Scope | Defines application in telecom-specific information security settings. | |
2 | Normative References | Lists ISO/IEC 27000-series standards for foundational alignment. | |
3 | Terms and Definitions | Provides telecom and cybersecurity-specific definitions. | |
4 | Structure of this Standard | Explains how ISO/IEC 27011 aligns with ISO/IEC 27002 and ISO/IEC 27001. | |
5 | Information Security Controls for Telecom Organisations | Core section with implementation guidelines based on ISO/IEC 27002. | |
6 | Sector-Specific Considerations | Details how telecom networks differ in threat exposure and control needs. | |
7 | Implementation Guidance | Practical methods for applying each control to telecom infrastructure. |
What are the requirements of ISO/IEC 27011?
Before implementing ISO/IEC 27011, it is important to understand the control expectations adapted from ISO/IEC 27002 and how they align with telecom-specific challenges. These controls cover operational security, network integrity, personnel practices, and infrastructure access. Below are some of the key requirements:
- Apply access control policies specific to network elements and subscriber data
- Secure the signalling systems (e.g., SS7, SIP, or Diameter) from external manipulation
- Protect physical telecom infrastructure, including towers and switches
- Implement audit logging and regular event correlation for telecom services
- Restrict administrative privileges and enforce role-based access
- Ensure resilience of telecom services against denial-of-service and other disruptions
- Control changes to telecom hardware and firmware, especially in live environments
To discuss certification or schedule an audit, contact us at support@pacificcert.com
What are the benefits of ISO/IEC 27011 Certification?
Before reviewing the specific benefits, it’s important to note that ISO/IEC 27011 brings telecom-specific relevance to general ISO/IEC 27001 controls. It helps organisations not only protect infrastructure but also manage sectoral risks unique to telecommunications, including interconnection fraud, SIM card cloning, and transmission snooping. Below are some of the key benefits:
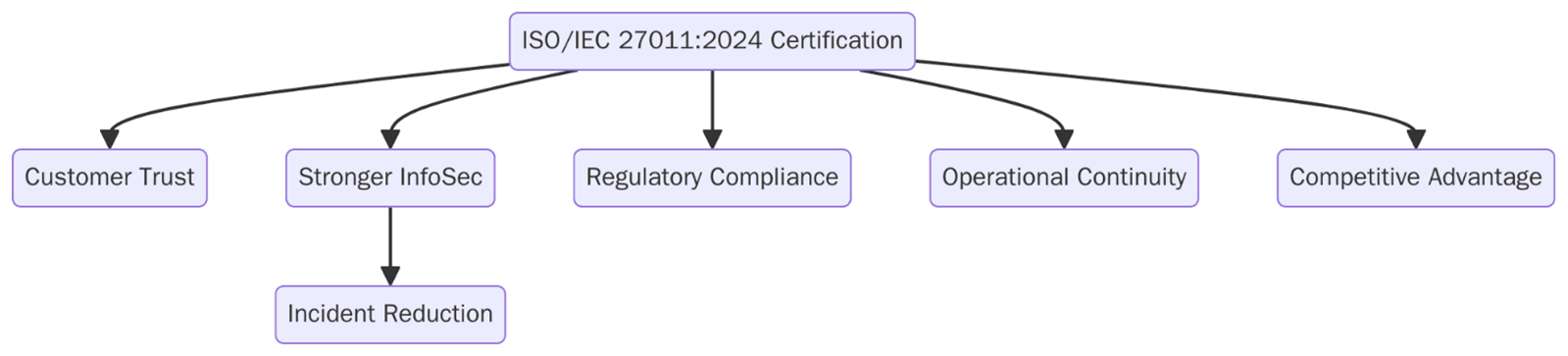
- Improved protection of signalling protocols and telecom transmission layers
- Stronger customer trust in network integrity and mobile communications
- Reduced risk exposure across roaming, interconnection, and vendor ecosystems
- Alignment with ISO/IEC 27001 for organisations already operating an ISMS
- Better control over network availability during maintenance and attacks
- Defined baseline for audits and internal security policies in telecom environments
- Recognition in RFPs and government contracts for telecom service providers
With the rise of 5G, IoT and edge computing, telecom infrastructure is becoming more vulnerable and complex. Operators are now expected to meet cross-border cybersecurity expectations while reducing downtime and misuse.
In the recent years, telecom regulators in several countries have aligned their baseline security requirements with ISO/IEC 27001 and ISO/IEC 27011, prompting both public and private providers to seek certification. There is also increasing demand from MVNOs and infrastructure sharing entities to adopt industry-accepted frameworks.
Audit Checklist
While ISO/IEC 27011 is not a certifiable standard on its own, it is used in tandem with ISO/IEC 27001 to shape security control implementation. The following checklist helps prepare for certification:
- Have cloud roles and responsibilities between the provider and customer been clearly defined and documented?
- Is virtual machine configuration securely managed and isolated in multi-tenant cloud environments?
- Are procedures in place for the secure return, deletion, or migration of customer assets after contract termination?
- Is administrative access by cloud service customers properly controlled and monitored by the provider?
- Are cloud-specific security requirements addressed in the service agreement (data location, jurisdiction etc.)?
- Is customer activity within the cloud environment logged, monitored, and reviewed for anomalies?
- Are customers informed of any changes that may affect cloud service security controls or SLAs?
- Are measures implemented to segregate and protect customer data in shared infrastructure setups?
- Is there a documented process for handling cloud-specific incidents and notifying affected parties?
Certification Process: ISO/IEC 27011 Integration with ISO/IEC 27001
To certify your ISMS that integrates ISO/IEC 27011 controls, the process involves:
- Gap Analysis – Identifying differences between your current security controls and the telecom-specific controls of ISO/IEC 27011
- Implementation Phase – Adjusting and tailoring ISO/IEC 27001 controls to align with ISO/IEC 27011 for telecom environments
- Internal Audit – Conducting pre-certification audits using sector-specific checklists
- Stage 1 Audit – Document review and readiness assessment by the certification body
- Stage 2 Audit – On-site verification of telecom-specific controls and ISMS effectiveness
- Certification Decision – Issuance of ISO/IEC 27001 certificate acknowledging ISO/IEC 27011 alignment
- Surveillance Audits – Conducted annually to maintain the certificate validity
Timeline
Implementation typically occurs in parallel with or following ISO/IEC 27011 adoption. The timeline for certification involves several phases. Preparation takes1-2 months for assessment, documentation gathering, and implementation of security measures. Audit takes another 1-2 months for the auditing process. Certification usually happens in 1 month after the audit. Ongoing Surveillance are the Annual audits to ensure continued compliance. Overall readiness usually achieved within 3–6 months, depending on organisational complexity and resource availability.
What is the cost of ISO/IEC 27011 Implementation?
The cost of ISO 27011 certification varies based on factors such as the size of the pipeline system, its complexity, and the number of facilities involved. Costs include Audit Fee which is the Fee for the certification body’s audit process. Training costs are the costs for educating staff on GDP Certification and the necessary processes for compliance. Ongoing maintenance are the costs for regular audits and recertification required every 3 years.
There is no separate certification fee as ISO/IEC 27011 is not a standalone certifiable standard.
How Pacific Certifications Can Help?
Pacific Certifications is an accredited certification body providing ISO/IEC 27001 certification with specific audit frameworks that account for ISO/IEC 27011 guidance. We assist telecom providers by:
- Reviewing telecom infrastructure against ISO/IEC 27011 control expectations
- Conducting audits that factor in sector-specific risks
- Offering integrated assessments for mobile, fixed, and hybrid operators
- Providing audit reports that highlight strengths and remediation areas
To align your telecom security practices with ISO/IEC 27011 and certify your ISMS, contact us at support@pacificcert.com
ISO/IEC 27011 Training and Courses
Various training programs are available to help teams understand and apply ISO/IEC 27011 controls within an ISO/IEC 27001 framework, such as:
- Lead Auditor Training – Equips professionals to conduct external third-party audits.
- Lead Implementer Training – For those responsible for planning and executing ISO/IEC 27011 implementation.
- Internal Auditor Training – Preparing internal auditors for certification audits
Pacific Certifications provides accredited training programs. If your organisation is looking for ISO/IEC 27011 training, our team is equipped to help you. Contact us at support@pacificcert.com
Frequently Asked Questions (FAQs)
Is ISO/IEC 27011 a certifiable standard?
No, ISO/IEC 27011 is not certifiable on its own but is used in conjunction with ISO/IEC 27001 certification for telecom-specific guidance.
Who should use ISO/IEC 27011?
Telecom service providers, ISPs, infrastructure vendors, and network operators who manage critical data and infrastructure.
Can ISO/IEC 27011 be applied outside the telecom sector?
The controls are tailored for telecommunications and may not be applicable in non-telecom industries.
Does it replace ISO/IEC 27001?
No, It supplements ISO/IEC 27001 by contextualising the controls from ISO/IEC 27002 for telecom use.
How is ISO/IEC 27011 different from ISO/IEC 27032?
ISO/IEC 27011 is focused on telecom security controls, while ISO/IEC 27032 provides general cybersecurity guidance for the internet and cyberspace.
Ready to get ISO 27011 certified?
Contact Pacific Certifications to begin your certification journey today!
Suggested Certifications –
Read more: Pacific Blogs






